Cloud storage security: top providers' security compared
Cloud storage security: top providers' security compared

The benefits of deject storage in an enterprise context are many, and most businesses today rely on it for some or all of their day-to-mean solar day operations. However, the shift from on-premises (on-prem) storage to the cloud presents new security risks alongside the benefits.
Cloud storage, when misused, can atomic number 82 to catastrophic data loss incidents, IP theft, or malware infection. The potential price to businesses is huge, and that's before we even consider the litigation that tin can emerge from these types of incidents.
Fortunately, the all-time cloud storage providers are highly secure and tin can almost guarantee that your business organisation won't endure fourth dimension-consuming and costly setbacks. This commodity compares cloud storage security beyond several categories, helping you determine which providers are the all-time cloud storage fit for your arrangement.
How to choose the most secure platform
Today, the cloud storage market is very competitive, and near of the top providers offer a like set of security features. Determining which platforms are the most secure requires an in-depth comparison across four categories: encryption, account security, back-up and geo-replication, and administrator controls - which is exactly what we will do here.
Encryption
Top-quality encryption is non-negotiable when it comes to secure deject storage, because it makes your data indecipherable to unauthorized persons.
AES (Advanced Encryption Standard) 256-bit encryption is an industry standard that can be used to protect data at balance (when stored on your provider's servers), while SSL/TLS (Secure Sockets Layer/Transport Layer Security) encryption (at either 128 or 256-chip AES standard) is commonly used to encrypt data in transit (when information is moving between servers).
As a full general dominion of pollex, 256-fleck AES encryption is more than secure than 128-bit. Cease-to-end encryption is the superlative level of encryption, ensuring only account users tin access data. This is achieved past providing the user with a set of encryption keys that are stored locally on the user'southward device.
To decrypt the information, the personalized encryption keys must be used, tying data access to trusted devices. Using finish-to-end encryption means that non even your provider can admission your files.
We recall the best providers are those that include unlimited stop-to-end encryption, such as pCloud and IDrive. pCloud includes finish-to-end encryption with all business plans, while IDrive enables administrators to manage their own encryption keys (thereby enabling end-to-end encryption). Read our pCloud review, our IDrive personal cloud fill-in review and our IDrive business review to learn more.
Microsoft OneDrive as well includes a feature called Vault, which is a sub-binder with end-to-end encryption. Unfortunately, though, files accept to be added i past one, making information technology a poor pick for use at an organization-wide level. Read our OneDrive review and our OneDrive for Business review to find out more about the service.
Providers such every bit Dropbox (256-bit at rest and 128-bit in transit), Google Drive (128-fleck at residuum and 256-fleck in transit), and Apple iCloud (128-bit both in transit and at rest) provide advanced levels of encryption, just without end-to-cease encryption. You tin acquire more near all three providers in our Dropbox review, our Dropbox for Business review, our Google Bulldoze review, and our iCloud review.
Business relationship security
No corporeality of encryption can protect your data if you or your employees' accounts are compromised. In one case a cybercriminal has accessed an employee'due south account, they tin access and edit all stored files that the employee has access to.
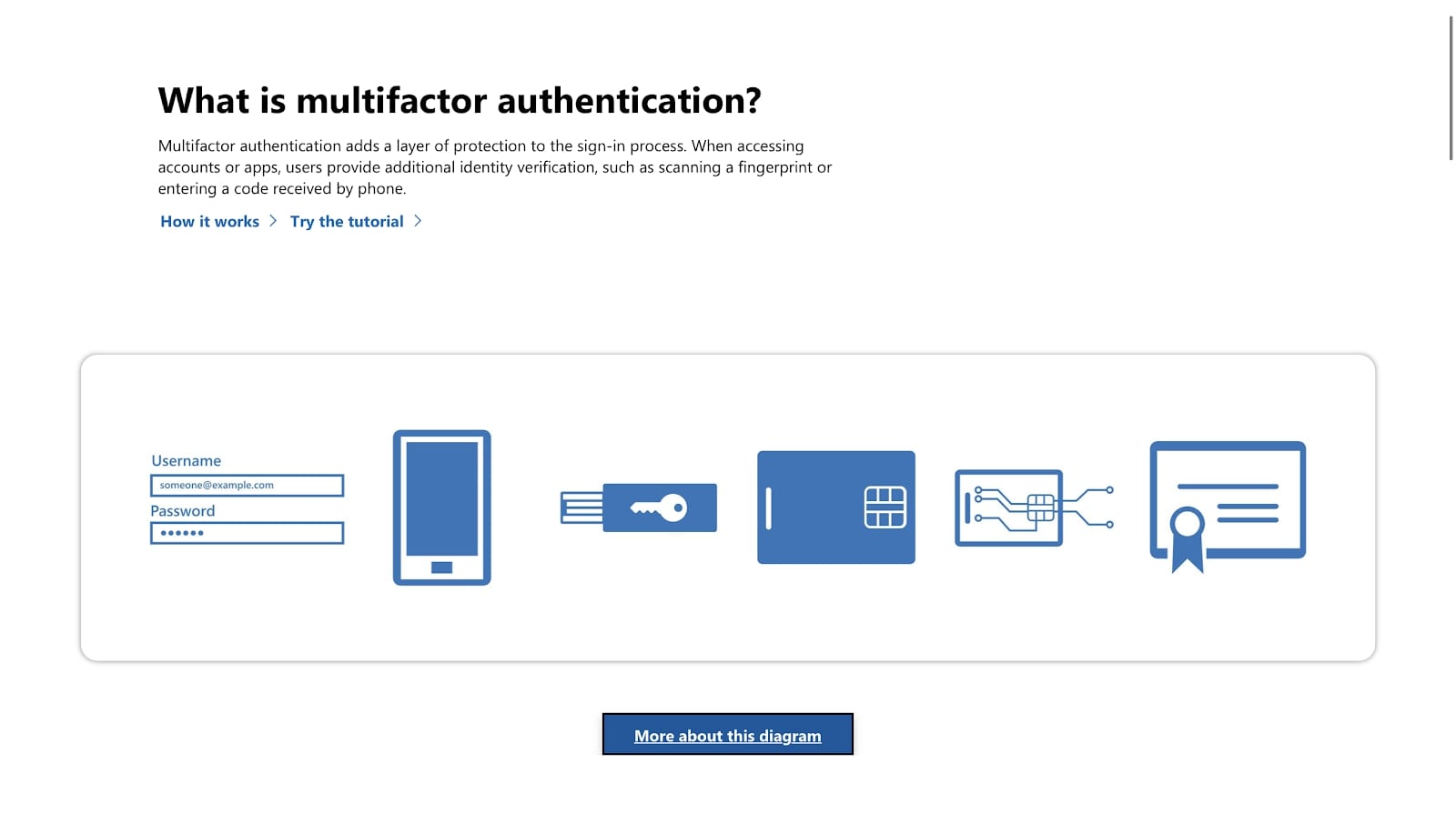
Business relationship security, therefore, is absolutely essential if y'all want to use cloud storage safely and securely. The nearly critical account security features are password standards enforcement, dictating how strong a password must be; and two-factor authentication (2FA), which adds a 2nd pillar of security to a user'south business relationship.
Password standards enforcement enables administrators to crave that all employee passwords meet specific criteria. Near commonly, these criteria will be a minimum password length and a requirement to include special characters. Insecure passwords are one of the meridian reasons that accounts are hacked, so requiring employees to create stiff ones is a unproblematic yet effective solution.
2FA is another security policy that is crucial for protecting employee accounts. Information technology requires employees to provide both a password and a secondary ways of authentication when logging into their business relationship. The 2d method is typically a code generated in an authenticator app or sent to the user's mobile or email accost. 2FA makes it extremely unlikely that your employee'southward account will be compromised.
Each of the seven platforms considered in this article provides both password standards enforcement and 2FA. However, we think Microsoft OneDrive and Google Drive earn actress points due to a more comprehensive 2FA framework across their range of software platforms.
Redundancy and geo-replication
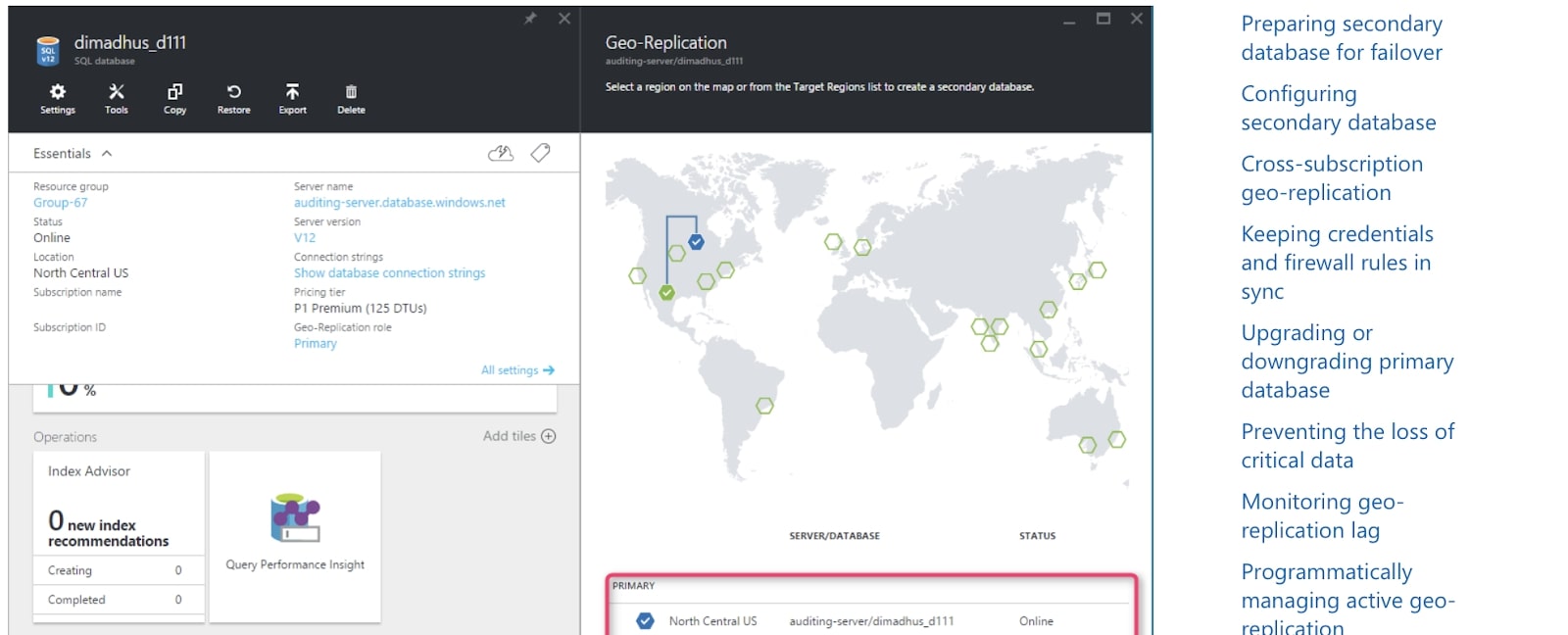
Organizations relying on cloud storage need to know their information volition always be available, even if at that place is a major disruption of service at a detail data heart or across an unabridged region.
The all-time cloud storage platforms have back-up policies beyond their networks, including geo-replication of information across several data centers and regions. This means that copies of your arrangement'due south information are stored across several locations, reducing the likelihood your data will be unavailable.
The marketplace leader in this expanse is undoubtedly Microsoft, with over 160 data centers in a truly impressive global network. Google is quite far backside with only 21 data centers. However, each of these information centres is a massive performance with hundreds of on-prem employees. In addition, both companies manage enterprise cloud storage solutions (Microsoft Azure and Google Deject) for large transnational corporations.
The other providers included in this commodity all provide some level of geo-replication and data redundancy, only the precise level of service is often unclear. It'southward besides important to mention that these providers usually don't own and maintain their own data centers, but contract out to 3rd-parties. This doesn't necessarily brand them less secure, but means there are more potential points of vulnerability.
Administrator controls

The concluding piece of the secure cloud storage puzzle is a robust suite of administrator controls. This is considering encryption, secure accounts, and robust data back-up policies corporeality to null if your employees misuse the platform, whether negligently or maliciously.
Therefore, all business owners should look for account auditing and office-based permissions in a secure cloud storage solution. Business relationship auditing enables administrators to generate usage reports quickly, and identify potential security risks before they become major issues. Audits also enable administrators to encounter which files are being accessed and by whom.
Role-based permissions enable business organisation leaders to control the types of files each employee has access to, allowing you to ensure sensitive or individual files are only accessible to those who need access.
Most of our providers offer an impressive suite of administrator controls, just we call up Dropbox stands out due to its dedicated admin console for all business customers. It goes higher up and across what is offered by the other platforms.
At the other cease of the spectrum, unfortunately, is Apple tree iCloud. Apple doesn't actually target its software to business owners, and so it often lacks when it comes to administrator controls.
Determination
In sum, to choose a secure deject storage platform for your business concern, you need to consider encryption, account security, back-up and geo-replication, and ambassador controls. The table below compares the platforms discussed in this article and their capabilities in relation to each of the points we've covered.
| Encryption | Business relationship security | Redundancy and geo-replication | Ambassador controls | |
|---|---|---|---|---|
| Microsoft OneDrive | A | A | A+ | A |
| IDrive | A | B+ | B | B+ |
| Google Drive | B- | A | A+ | B+ |
| Apple iCloud | A- | B+ | B | C |
| Dropbox | B | B+ | B | A+ |
| pCloud | A+ | A+ | B | B |
It is merely when y'all compare providers beyond these categories that the best platform for your individual needs will become apparent. Taking the time to find a platform that will integrate seamlessly into your organization is a decision that volition pay dividends for many years to come.
Larn more about cloud storage security in a range of our features focusing on the subject, including: why deject storage is secure, featuring tips on how to utilise it securely; and what you should look for in secure cloud systems.
Source: https://www.tomsguide.com/features/cloud-storage-security-top-cloud-providers-security-compared
Posted by: johnsonandoulte.blogspot.com


0 Response to "Cloud storage security: top providers' security compared"
Post a Comment